BSides Munich 2019 Recap
Between the 24th and 25th of March I participated in the BSides Conference and Workshops, this piece presents a short recapitulation of what I saw, learned and liked about the event.
My journey started in the middle of January when I filled out the call for papers and workshops. The goal present a one day workshop to give back to the security community and test some new hands-on exercises and slides on wireless hacking. About one month later I received a friendly acceptance email.
Day one: workshop
As always, some things kept me working until well into the night a couple of days before the event. But finally, left for the workshop on the Sunday at 3:30 am. I got to the venue on time, even though I had planned a buffer just in case.
Everything was very well organized. I picked up my credentials and made my way to the classroom. The location, was the brand new office of the TÜV SÜD in Munich. The meeting rooms even had the protective plastics on.
I was lucky to have the biggest group, 16 participants with different backgrounds and experience levels. From experienced pentesters and security experts in other domains to college students. Did I mention that the event, including my workshop was sold out in less than two hours!
We pretty much went through the material as planned, covering an introduction to SDR and radio waves. We covered some tools like gnuradio and RTL-SDR and then dove into working with universal radio hacker (urh). I did manage to get some Yardstick Ones delivered on time for the event, so we practiced capturing and sending information with them. We closed, by reverse engineering the signals from a couple temperature sensors working in the ISM bands.
The direct feedback was great. All participants said that it was worth investing the day indoors, even though there was gorgeous weather outside. I’m happy that the new content, especially the hands-on exercises, were as educational as I expected.
The conference was as well organized as the workshops. The team got everyone checked in pretty quickly, paths were pretty clear on where to go for the talks and they even did a simultaneous broadcast from the main auditorium into the smaller Moonshot Track room.
As all conferences it is very hard to pick which talks to attend, you never know all the variables: Is the speaker good? Can he deliver his message? Will it be edutaining or will I be bored to death? Will I actually learn something about the topic? In which talk will I gain the knowledge nuget I came for?
The best talks I saw on site were the following:
Stu and Tash delivered a really cool talk. They shared the little secrets that have allowed
them to build and motivate an external team to support their efforts. Since they are the only dedicated FTE’s working on security they depend a lot on management, IT and developers to help them get anything done.
Aaron presented a really good talk: to the point and filled with actionable information on how to build a system that allows you to create forensic timelines and detect security issues.
Sebastian talked about his experience doing offensive security for an automotive OEM (car manufacturer in automove lingo). He presented the challenges of the industry, timelines and how it has evolved in the last couple of years. The high level overview of the testing methodology, tools and required knowledge, were really good.
For me it was very interesting to see how testing a car is not very different than the work I do in IoT.
In parallel to the conference, there was a Capture the Flag (CtF) event. I always find it pretty hard to do a conference and the CtF at the same time. So I normally try to do the conference and pick my brain with the challenges when I get bored. One of the highlights, were the IoT challenges. These went from a voice powered interface to UART hacking of microcontrollers.
Summary
To sum up the event in a couple of sentences. It was very good in content and organization. The team was very friendly and did a great job to make it a smooth experience. I will come back next year. Look for the slides and recording to all the talks on the BSidesMuc Website.



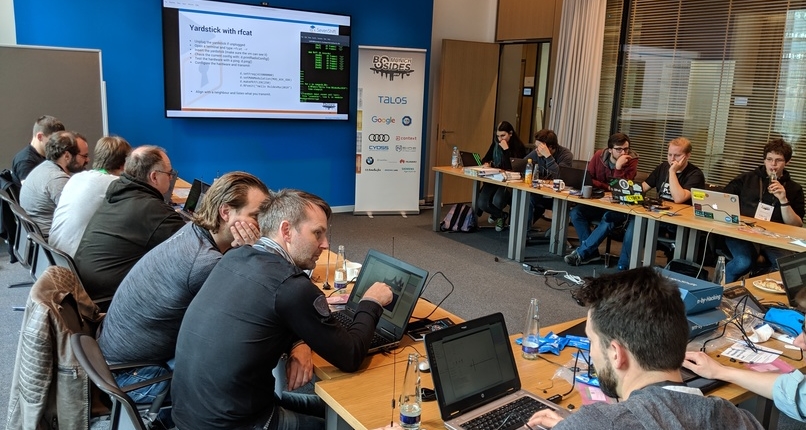

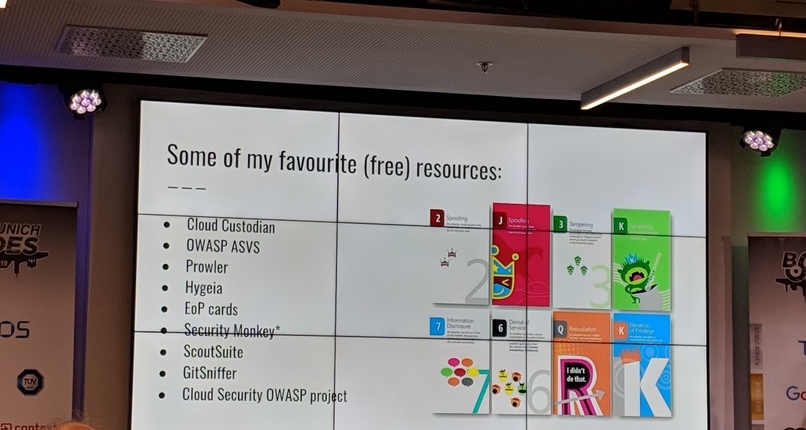
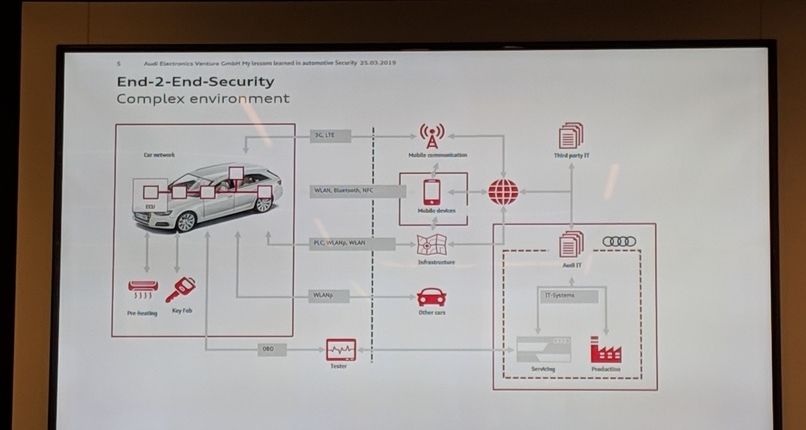
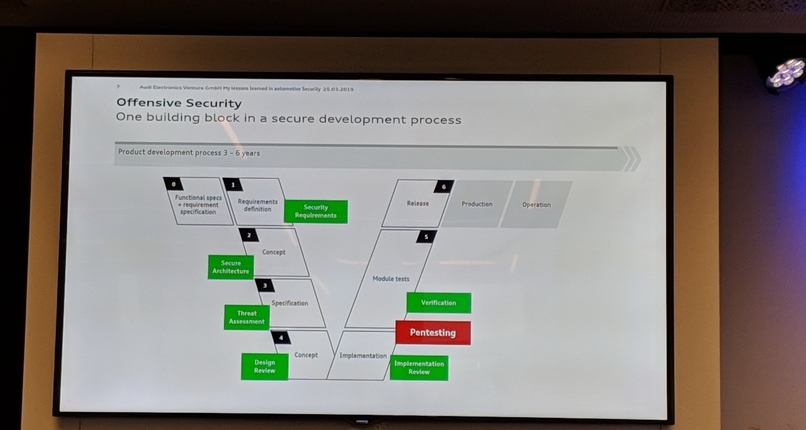
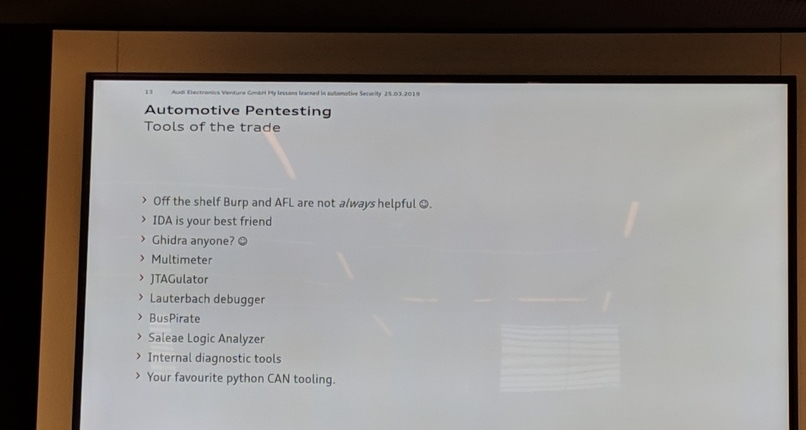

 Photo by Braden Collum on Unsplash
Photo by Braden Collum on Unsplash Foto credit: ken-yam-1152004-unsplash
Foto credit: ken-yam-1152004-unsplash